Ledger Login: Unlocking the Safest Way to Access Your Crypto
The Ledger login process brings together convenience and hardware-level protection to give you total control of your digital assets — no passwords, no risks, just pure security.
Understanding the Ledger Login System
Unlike conventional accounts that depend on usernames and passwords, the Ledger login process is built on device authentication. This means you confirm actions physically through your Ledger hardware wallet — a secure chip-based device that keeps your private keys offline. The login is, in essence, a digital handshake between Ledger Live (the software) and your Ledger device (the hardware), ensuring your funds remain inaccessible to anyone else.
This model of access represents the future of secure finance — one where users manage their assets without depending on centralized services that store sensitive data on servers.
The Purpose Behind Ledger Login
Ledger Login is designed to achieve one main goal: security through ownership. Instead of “logging in” to a remote account, you’re verifying access locally through your hardware wallet. Here’s what makes it exceptional:
- ✔️ Decentralized Authentication — Only your device can authorize access, eliminating phishing and credential theft.
- ✔️ Cold Storage Integration — Keeps your keys offline and immune to malware attacks.
- ✔️ Hardware Verification — Every transaction and connection must be physically confirmed on your device.
- ✔️ Cross-Platform Access — Seamlessly connects via desktop or mobile Ledger Live app.
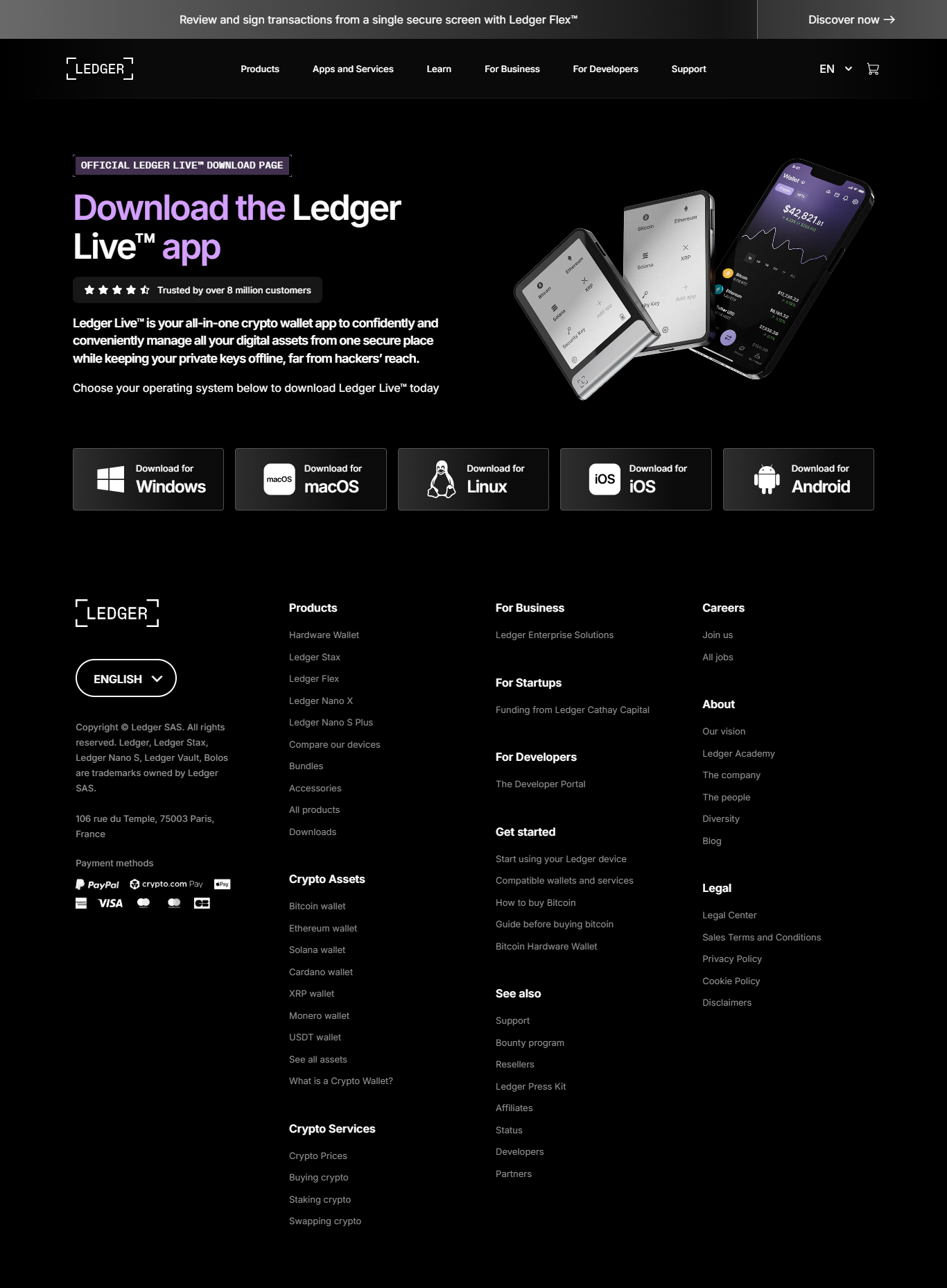
1️⃣ Step 1: Install Ledger Live
Download the official Ledger Live app from Ledger.com. Choose the correct version for Windows, macOS, Linux, or mobile.
2️⃣ Step 2: Connect Your Ledger Device
Plug in or pair your Ledger Nano X, S Plus, or Stax. The device will prompt you to confirm connection security.
3️⃣ Step 3: Verify & Access
Open Ledger Live, verify the connection, and unlock instant access to your portfolio and transaction features.
Benefits of Ledger Login Over Traditional Crypto Accounts
Traditional crypto exchanges and wallets often rely on email and password systems — which are vulnerable to phishing, leaks, and brute-force attacks. Ledger login removes those risks entirely. Here’s how it stands apart:
| Feature | Ledger Login | Exchange Login |
|---|---|---|
| Security Level | Offline, device-based confirmation | Online, password-based access |
| Data Ownership | You control private keys | Exchange holds your data |
| Login Risk | Virtually zero (hardware verified) | High (password leaks/phishing) |
| Recovery | 24-word seed phrase | Email-based reset |
Troubleshooting Ledger Login Problems
1. Ledger Not Detected
Ensure your cable supports data transfer and that your device is unlocked. Try using a different USB port or restart Ledger Live.
2. “Device Not Genuine” Error
Update your device firmware and reattempt verification. Ledger checks cryptographic authenticity before login.
3. App Sync Delays
Slow syncing often comes from outdated software or network issues. Always install the latest Ledger Live version.
4. Forgotten PIN
Use your recovery phrase to reset your Ledger device and create a new PIN. Your funds remain intact on the blockchain.
Top Security Tips for Ledger Login
- ✅ Always verify you’re using the official Ledger Live app — avoid fake websites or app stores.
- ✅ Keep your recovery phrase offline and never store it digitally.
- ✅ Regularly update your Ledger firmware and Ledger Live software.
- ✅ Double-check transaction addresses before approving on the device.
- ✅ Use the “Advanced Logs” section in Ledger Live to monitor connection events.
FAQs About Ledger Login
1. Do I need the internet to use Ledger Login?
Yes, an internet connection is required for blockchain access, but your keys remain offline during every session.
2. Can someone hack Ledger Login remotely?
No. Since every action requires a physical device confirmation, remote hacks are virtually impossible.
3. Is Ledger Login compatible with mobile?
Yes. The Ledger Live mobile app supports secure Bluetooth login with the Ledger Nano X and Ledger Stax.
4. What if I lose my Ledger device?
Use your recovery phrase to restore your account on a new Ledger wallet. The Ledger login process will rebind automatically.
Conclusion: Ledger Login Is Your Key to True Financial Autonomy
The Ledger login experience represents a new era of crypto access — one where convenience meets unbreakable security. By combining Ledger Live with hardware authentication, users enjoy effortless control over their funds without surrendering privacy or trust.
With Ledger Login, you hold the key to your digital assets — literally and securely.